Visual Guide
The path at a glance
SecurityRecipes is meant to be read as a loop:
- Find the right entry point.
- Run one small, reviewer-gated remediation PR.
- Turn the pattern into a security-operated workflow.
- Add MCP context, policy, and audit when the workflow needs to scale.
1. Start with the map

If you are brand new, begin with Quick Start. If you already know the task, search directly for an agent, CVE, MCP connector, prompt, or workflow. The site is intentionally structured so you do not have to read everything before doing something useful.
2. Run one safe agent PR

For the first run, choose the AI coding tool your team already has: GitHub Copilot, Devin, Cursor, Codex, or Claude. Copy the matching house-rules file from the agent recipe or prompt library, give the agent one small finding, and review the pull request like any other change.
3. Operate remediation as a workflow

Once one PR works, graduate to the Security Remediation section. The workflows there show how to decide which findings are eligible, what files the agent may touch, what evidence the run must produce, and where the agent must stop instead of guessing.
4. Use MCP as the context layer
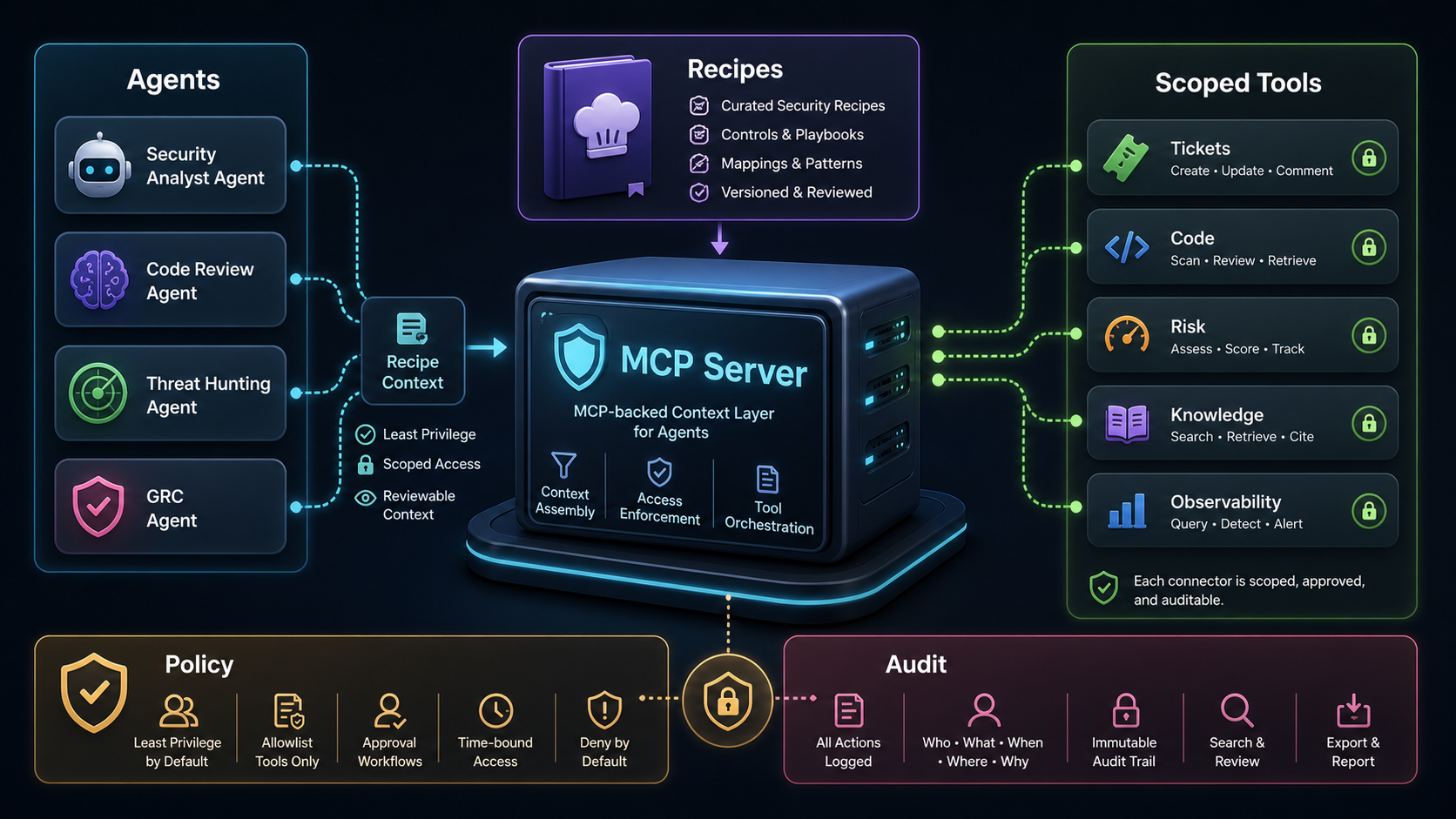
The production shape is MCP-backed. Agents retrieve recipe context from the site or MCP server, policy narrows which tools they may call, scoped connectors reach enterprise systems, and audit records keep the run reviewable.
What to read next
- Quick Start if you want the shortest path to a first PR.
- Agents if you already know which AI tool your team uses.
- Prompt Library if you need rules, skills, or prompts to copy into a repo.
- MCP Servers if you need controlled context and enterprise connectors.
- Security Remediation if you are designing the full security-operated workflow.